Maritime cyberattacks surged in 2025, fueled by ransomware and DDoS incidents, warns Cytur, highlighting vulnerabilities in shipping security.
The prevalence of maritime cyberattacks doubled last year, driven by ransomware and distributed denial of service incidents, reported Fort Lauderdale's Maritime Executive. Korean security firm Cytur stated that hackers are increasingly targeting shipping for financial gain.
Cytur noted that attackers often exploit crew members through phishing emails, unsecured public Wi-Fi, or infected USB drives. Stolen data, such as voyage logs, cargo manifests, and crew details, is sold on the Dark Web, while ransomware frequently encrypts ship systems, forcing operators to pay to regain access.
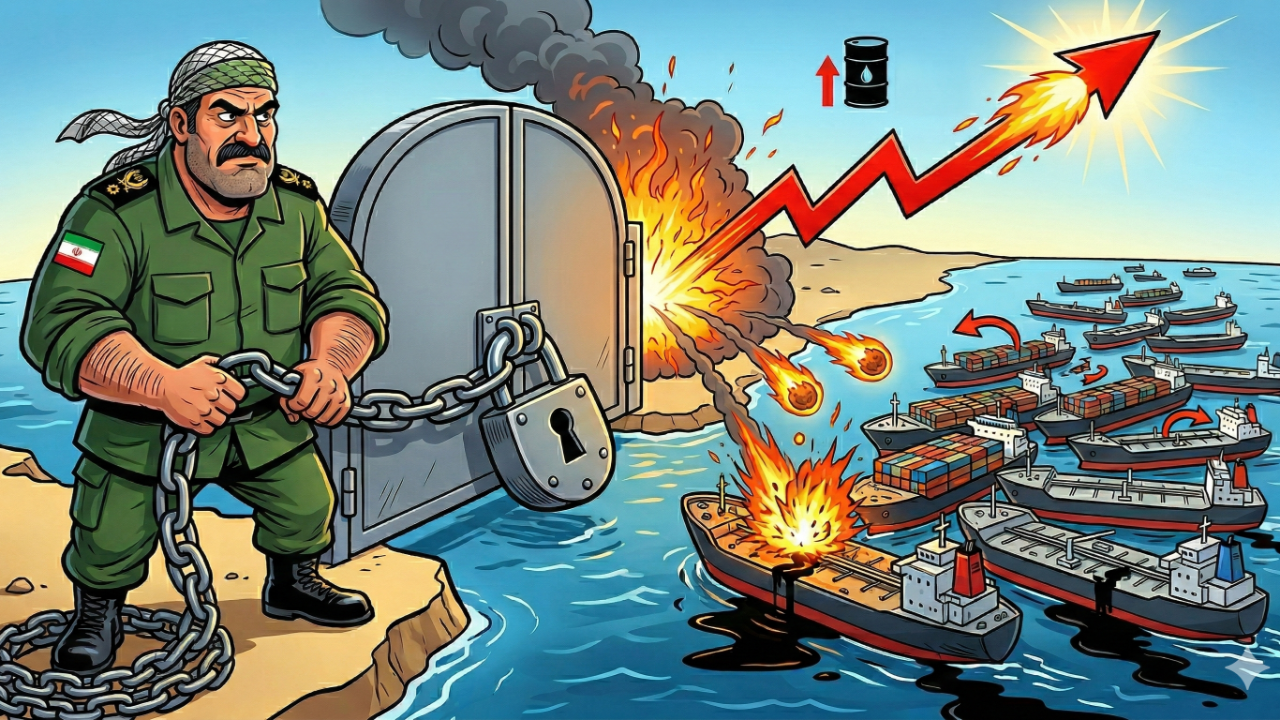
Distributed denial of service attacks are also common, overwhelming satellite communication connections by hijacking onboard routers. More advanced supply chain breaches included the Lab Dookhtegan attack on Iranian satcom provider Fanava, which disrupted tanker communications and destroyed ship modems.
In October, Japanese radar and ECDIS (Electronic Chart Display and Information System) maker Furuno was hit by ransomware from the Rhysida group, which stole data, disabled backups, and demanded payment. Cytur warned that operating technology, such as engine controls and ballast systems, remains vulnerable to remote manipulation.
Cytur predicted that AI-assisted hacking will rise, ushering in autonomous attacks that lower the skill barrier for cybercrime. 'Maritime cybersecurity is no longer an option but a matter directly linked to a vessel's right to operate,' said Cho Yong Hyun, the firm's chief executive.